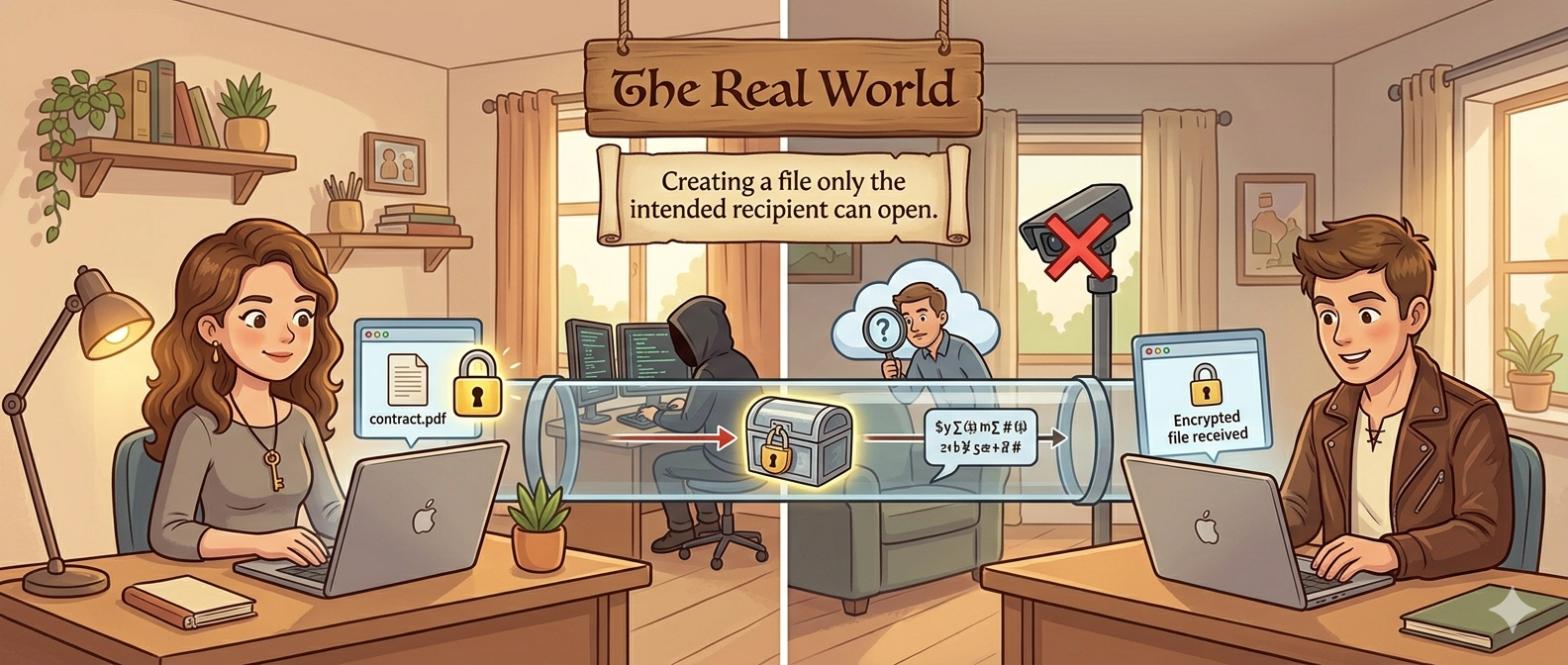
How Do You Send a Secret Nobody Else Can Read?
Every file you send online passes through dozens of hands before it reaches the other person. Here's why that's a problem — and how to solve it.
Your files pass through strangers
When you send a file to someone over the internet, it doesn't travel directly. It hops through Wi-Fi routers, internet service providers, cloud servers, and email relays. At every stop, someone — a hacker, a compromised server, a curious admin — could intercept and read it. Normal email and file sharing offer no protection.
Wi-Fi sniffing
Server breaches
Surveillance
Interception
Now Imagine the Same Problem, Centuries Ago
To understand the solution, let's tell the story a different way — with padlocks, sealed letters, and a town full of curious couriers.
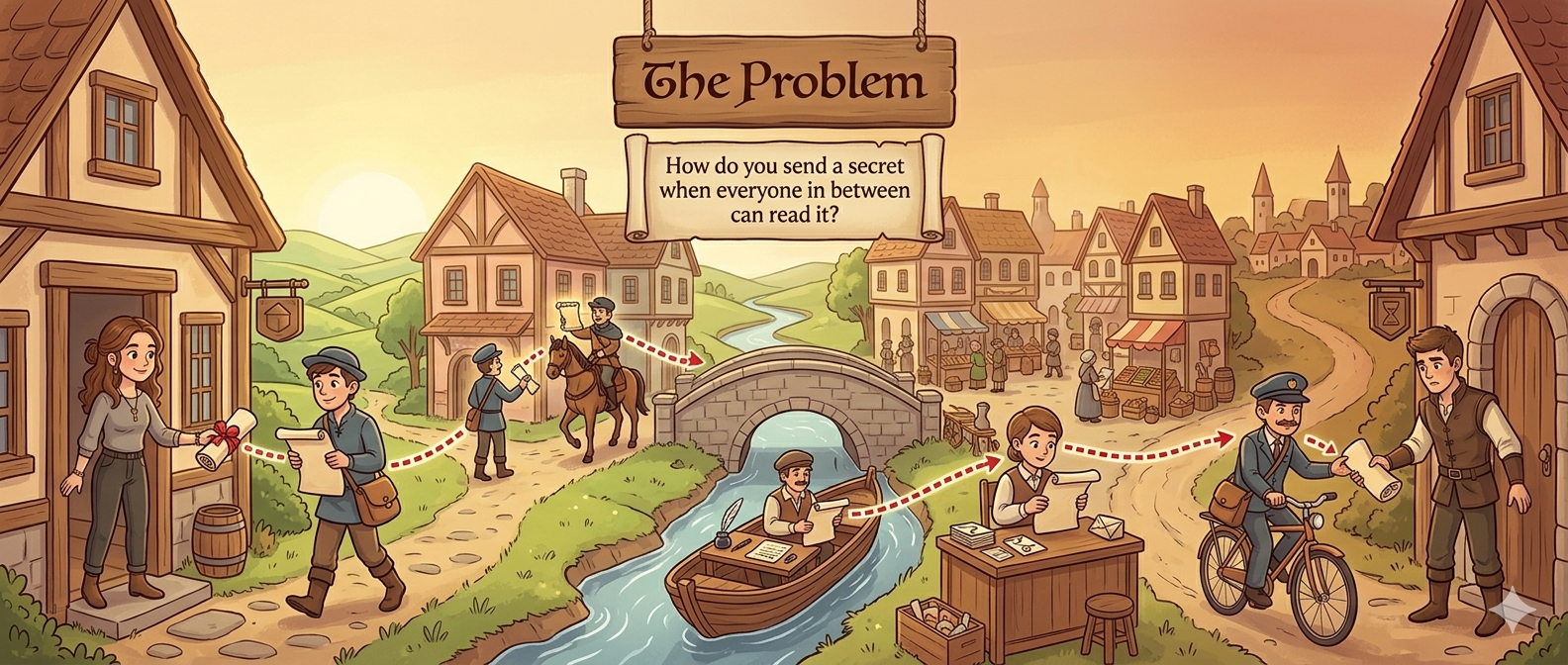
A secret that passes through five hands
Alice needs to send a confidential scroll to Bob. But the journey is long — it passes through a village messenger, a horseback courier, a river barge operator, a postal clerk, and a delivery boy. Every single person unfolds it and reads every word. By the time it reaches Bob, the secret is no longer a secret.
Peeking
Copying
Tampering
The Padlock Solution
What if you could lock a box so securely that only the intended person could ever open it — even if every courier along the way tried?
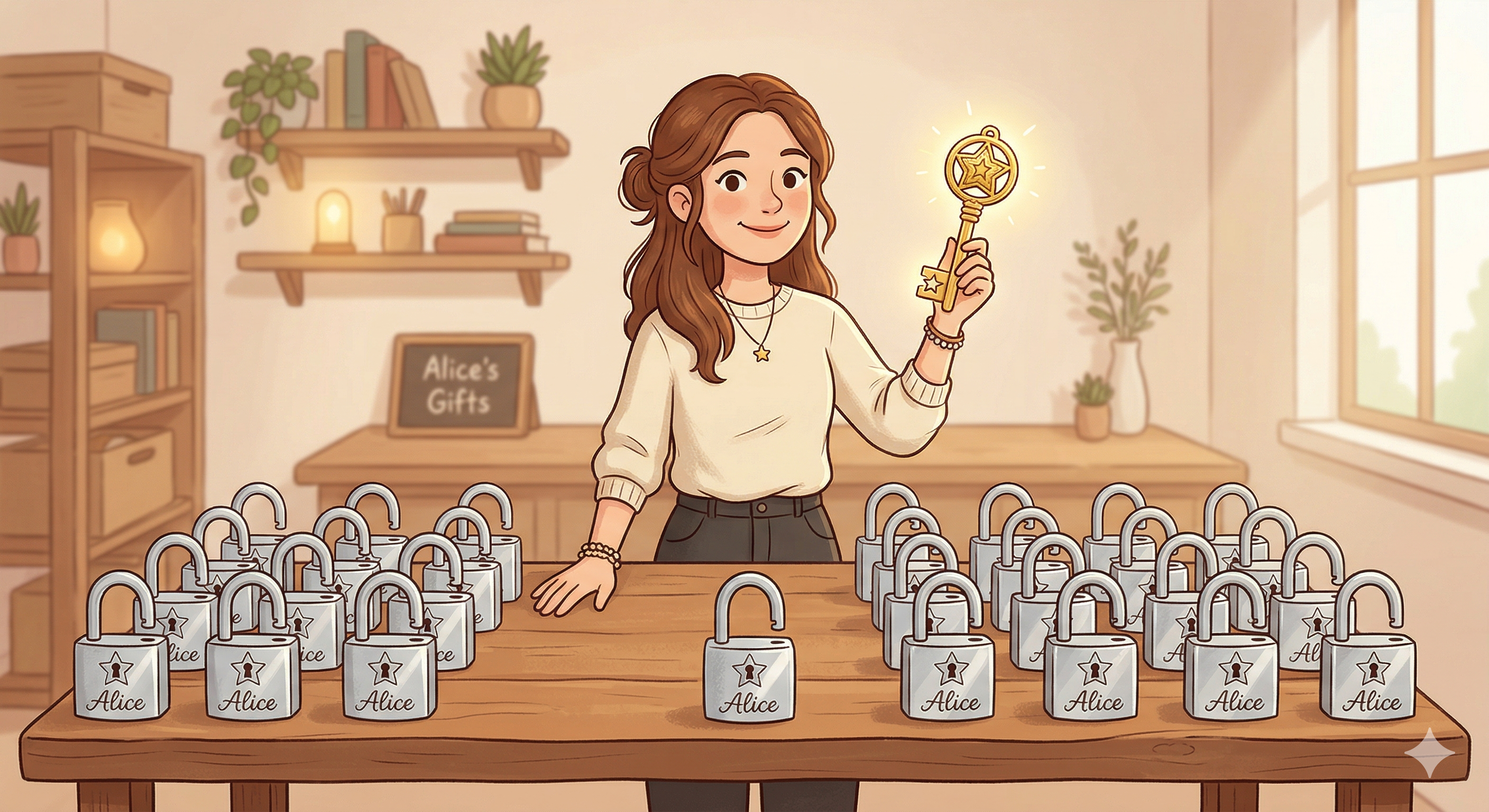
Everyone Makes a Padlock and a Key
Alice creates a golden key that only she keeps, and many identical padlocks she can share with anyone. Her golden key is the only thing in the world that can open her padlocks.
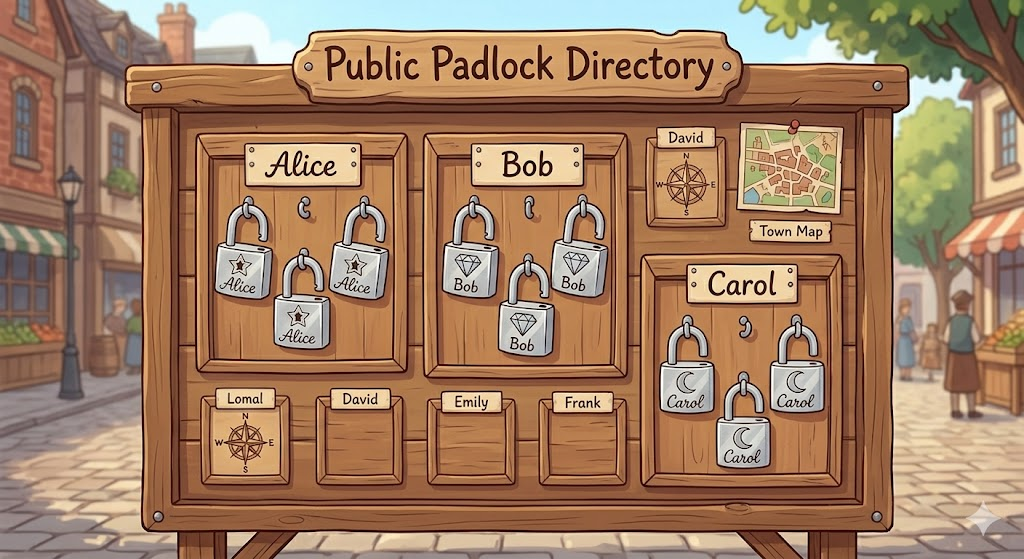
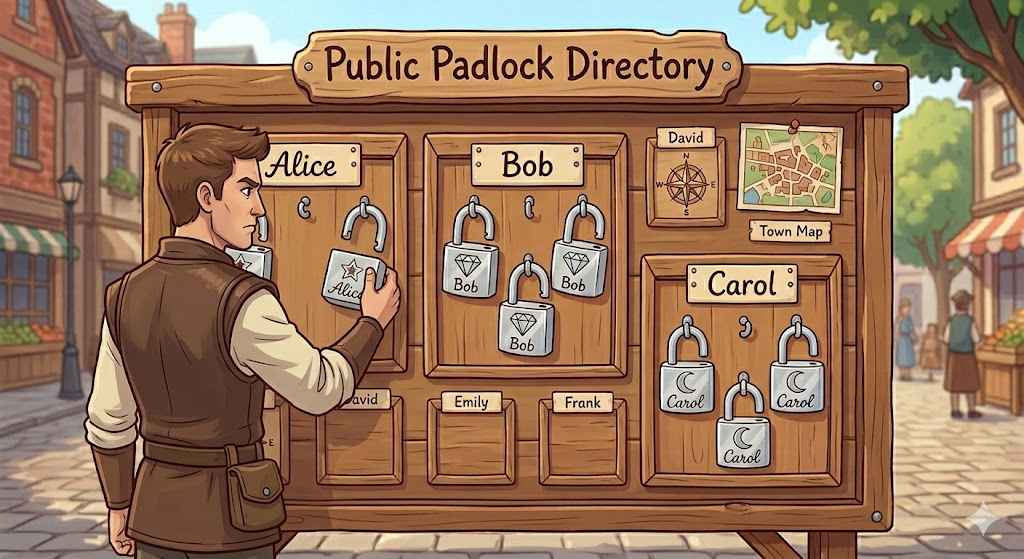
Padlocks Go on a Public Board
Alice hangs her padlocks on a public board in the town square. Bob, Carol, and others do the same. Anyone who wants to send someone a secret can grab their padlock from the board.
Bob Grabs Alice's Padlock
Bob wants to send Alice a secret document. He visits the board and picks up one of Alice's padlocks. He checks the unique marking engraved on it to make sure it really belongs to Alice.

Bob Stamps His Wax Seal
Before sealing the document, Bob presses his own unique wax seal onto it. Nobody else has his seal — so when Alice sees it later, she'll know for certain the document came from Bob and hasn't been touched.

Bob Locks the Box with Alice's Padlock
Bob places the sealed document into a sturdy metal box and snaps Alice's padlock shut. The box is now locked. Even Bob can't open it anymore — only Alice's golden key can.

The Locked Box Travels Across Town
A courier carries the locked box through busy streets, crowded markets, and past nosy neighbours. None of it matters — the box is locked tight and the contents are completely hidden from everyone who handles it.

A Thief Tries and Fails
A shadowy figure intercepts the box and tries every key they own. Nothing works. Without Alice's specific golden key, the padlock won't budge. The thief is left surrounded by useless keys.

Alice Opens the Box
The box arrives at Alice's workshop. She takes out her golden key — the only key in the world that fits her padlocks — and opens the lock. The document inside is perfectly intact.

Alice Checks Bob's Seal
Alice examines the wax seal and compares it to Bob's known pattern. It matches. She now knows two things: the document definitely came from Bob, and nobody changed it along the way.
This Is Exactly What CryptDrop Does
That padlock story isn't just a metaphor — it's precisely how modern encryption works. The technology behind it is called OpenPGP (Pretty Good Privacy), and CryptDrop puts it right in your browser.
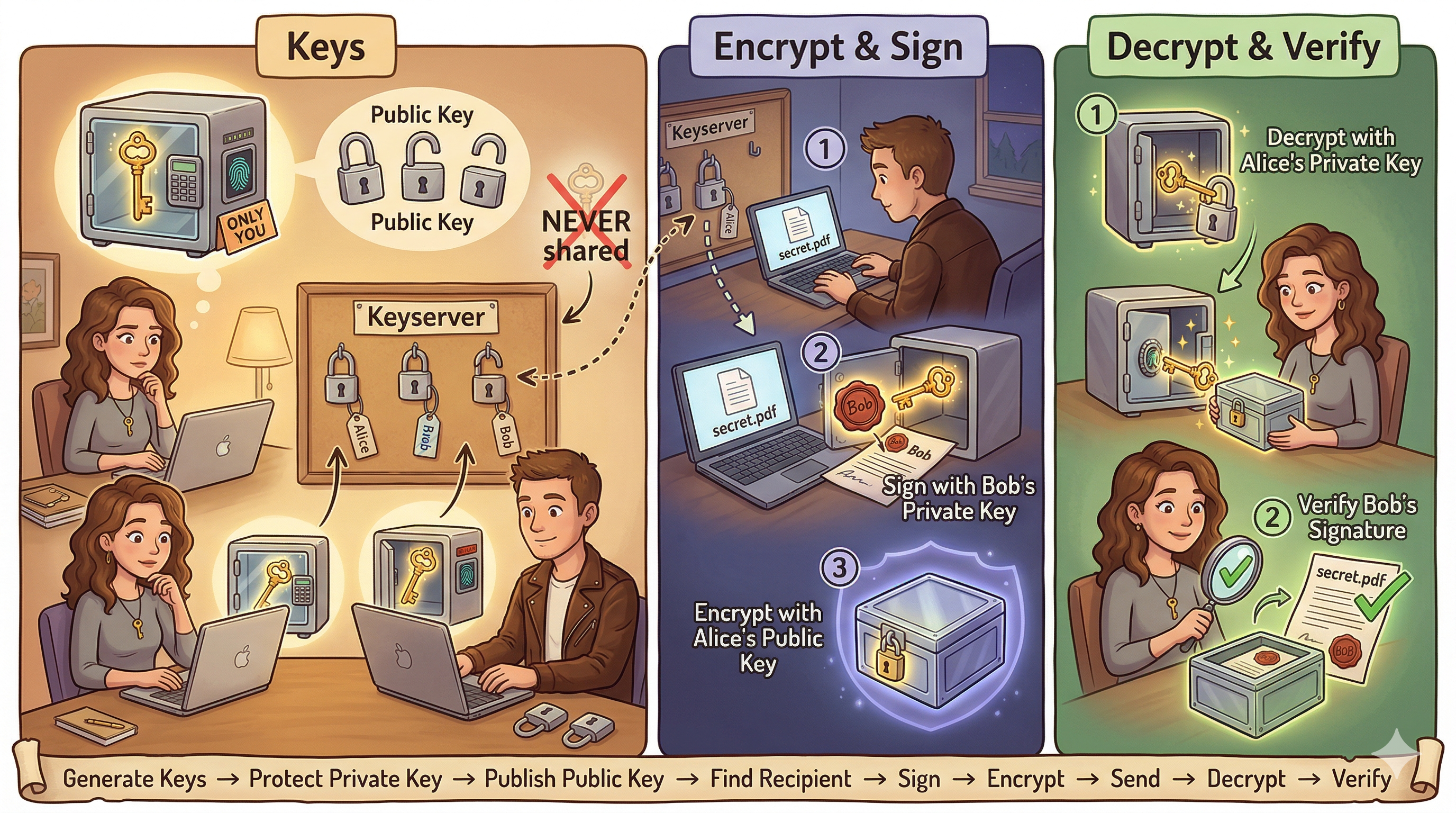
Same idea. Modern magic.
Every step in the padlock story maps directly to something CryptDrop does. You generate keys, find recipients on a public keyserver, encrypt files that only they can open, and verify who sent them — all without anything ever leaving your device.
| In the Story | In CryptDrop | What It Does |
|---|---|---|
| Padlock | Public Key | Shared openly so anyone can encrypt a file for you |
| Golden Key | Private Key | Kept secret — the only thing that can decrypt your files |
| Wax Seal | Digital Signature | Proves who sent the file and that it wasn't tampered with |
| Locked Box | Encrypted File (.pgp) | The scrambled file that's safe to send over any channel |
| Public Board | Keyserver | A directory where people publish their public keys |
| Town Courier | The Internet | The untrusted path between sender and recipient |
Ready to Send Your First Secret?
No installs. No sign-ups. No servers. Everything happens right here in your browser.
Open CryptDrop →